The CISO in the modern digital world will need to take responsibility for guarding an organisation’s crown jewels as a condition within his job role.
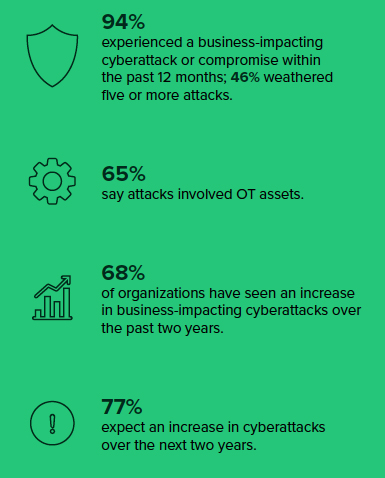
Tenable has published a global industry study that revealed, 95% of Saudi Arabian organisations have experienced a business-impacting cyberattack in the past 12 months. The data is drawn from, The Rise of the Business-Aligned Security Executive, a commissioned study of more than 800 global business and cybersecurity leaders, including 49 respondents in Saudi Arabia, conducted by Forrester Consulting on behalf of Tenable.
As cybercriminals continue their relentless attacks, 85% of respondents in Saudi Arabia have witnessed an increase in the number of business-impacting cyberattacks over the past two years. Unfortunately, these attacks had damaging effects, with organisations reporting loss of customer or employee data 41%, ransomware payments 37% and financial loss or theft 35%. Roughly 61% security leaders in Saudi Arabia say these attacks also involved operational technology.
Business leaders want a clear picture of how at risk they are and how that risk is changing as they plan and execute business strategies. But only four out of 10, local security leaders say they can answer the fundamental question, with a high level of confidence: How secure, or at risk, are we?
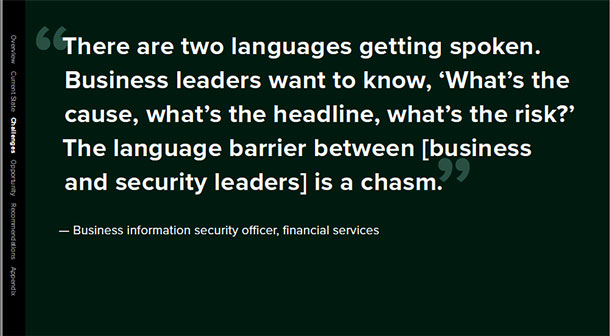
Looking at global respondents, fewer than 50% of security leaders said they are framing cybersecurity threats within the context of a specific business risk. 96% of respondents had developed response strategies to the Covid-19 pandemic, but 75% of business and security leaders admitted their response strategies were somewhat aligned.
Organisations with security and business leaders who are aligned in measuring and managing cybersecurity as a strategic business risk deliver demonstrable results. In the future, there may be two kinds of CISOs. Those who align with the business and everyone else. The only way to thrive in this era of digital acceleration is to bring cyber into every business question, decision and investment.
Vulnerability mapping
Tenable’s core engine is Nessus and that is the largest source of vulnerability assessment tools. The core solution benefits from Tenable are around vulnerability management. Tenable scans networks, systems, applications and tells the customer whether they are vulnerable on those systems. After this, the end customer can mitigate the risk of being hacked by applying specific measures to those systems to make sure they are not vulnerable to cyberattacks.
Nessus is used globally and Tenable has intelligence not only on existing vulnerabilities but also feeds from vulnerabilities that will be exploited in the coming days. It is collected through manual and automated processes as well. It is like a hybrid mode, it is not fully manual, and it is not fully automated.
Tenable’s focus is on enterprises, regardless of whether it is government or private, small, medium, or large. What matters is that the company cares about its intellectual property, its customer records, financial data or any confidential data. “That is our core competence,” says Maher Jadallah, Regional Director, Middle East, Tenable.
Asset mapping
Each customer values their data in their own way. The process of mapping the criticality of an asset on the network is done jointly with the business and the organisation’s cyber security team. The criticality of an asset varies by organisation and by industry. Tenable solutions need to be used by an organisation’s CISO to ensure that the organisation’s crown jewels as defined by business are protected.
 Jadallah points out that inside an organisation, business looks at the criticality of an asset typically through two aspects. It could be either through the ability to make profits, if it is highly accountable on making profits. And the other is through its repository of data. Here, data could have many forms such as customer profile data, transaction data, or patient medical records as an example.
Jadallah points out that inside an organisation, business looks at the criticality of an asset typically through two aspects. It could be either through the ability to make profits, if it is highly accountable on making profits. And the other is through its repository of data. Here, data could have many forms such as customer profile data, transaction data, or patient medical records as an example.
A typical legacy cyber security application does not map assets based on the criticality for business. “A legacy system will not look into the business impact but at Tenable we map security vulnerability to asset criticality. If the asset is critical, we give it a different flag,” says Jadallah.
If an asset is flagged as business critical and has a high vulnerability exposure, it is flagged to the CISO. “I call it prioritisation. I need to prioritise my remediation plan towards those critical assets. That is why Tenable addresses this well because we map vulnerabilities to critical assets to business,” says Jadallah.
When a CISO sits with business and understands the drivers, the mission and what the customer cares about, they can map that into the configurations of the existing security system. They have to sit together to become more aligned. By sitting together, their strategy begins to match the goal of the company.
CISOs who operate in their individual silo are not part of tomorrow’s landscape. They will need to be able to speak the language of business.
This is an upgrade to the typical CISO role, feels Jadallah. “Today, a typical CISO, will not last long. We need CISOs today that are more aligned to the business and speak the language of business. That is the kind of modern CISO required for the future.”
Targeting operational technology
According to the recent Tenable survey, 61% security leaders in Saudi Arabia say attacks also involved operational technology. Inside the realm of operational technology, devices and systems are not subject to continuous upgrades as in the information technology realm. In some cases, the system may not have been updated for more than 10-20 years. Since it is an old system, that has not been patched it is highly vulnerable to hacking, even through the most basic hacking tools.
On the information technology side, devices, systems, and applications are being continuously patched and updated. And hackers would prefer to move laterally towards the operational technology side. “It is easier for me to go through an old and neglected system, than a dynamic network that is always updated and protected,” points out Jadallah.
The weak link in the chain, is that operational technology workers are also on the same organisational network as rest of the employees, and use the same tools as rest of the organisation. Any employee that has access to operational technology systems or is connected to an operational technology device, is therefore a priority subject to be compromised.
They also log in directly into air-gapped operational technology systems to manage them as required. Target the operational technology teams, compromise the administrator and you can get access to the operational technology systems.
In reality today, threat actors are targeting the operational technology side, because the compromise can be demolishing and a backbone breaker, according to Jadallah. Not all cybersecurity systems can provide an integrated view of asset criticalities and security vulnerabilities, across the complete organisation.
“You need a system that can give you cyber exposure after all these modern assets are connected to each other. You need a system or tool that will help you to find vulnerabilities on that interconnected network,” he stresses.
The survey
The Tenable commissioned study was executed by Forrester Consulting through an online survey of 416 security and 425 business executives, as well as telephonic interviews with five business and security executives. It examined cybersecurity strategies and practices at midsize to large enterprises in Australia, Brazil, France, Germany, India, Japan, Mexico, Saudi Arabia, the UK and the US. The study was conducted in April 2020.
Attributes of business-aligned security leaders
- Confident in their ability to report on level of risk to organisation
- Demonstrate cybersecurity investments are positively impacting business performance
- Use metrics to track cybersecurity ROI and impact on business performance
- Cybersecurity objectives are in lock step with business priorities
- Holistic understanding of organisations entire attack surface
- Asset criticality and vulnerability data when prioritising remediation